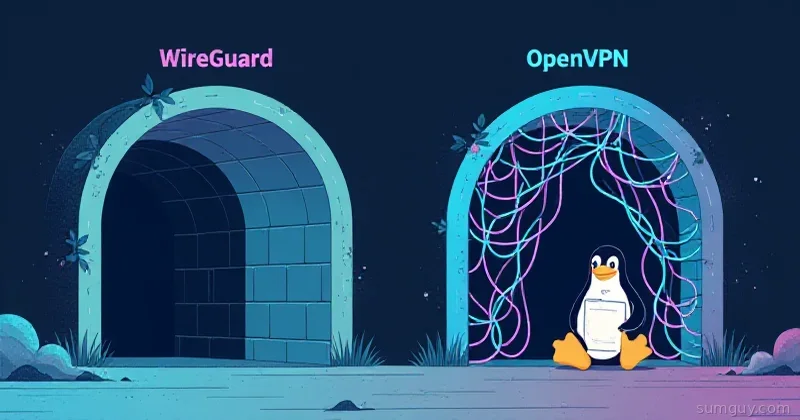
The Old Guard vs The Newcomer
Here’s the thing: OpenVPN has been the default home-lab VPN for two decades. It works everywhere, runs on everything from a Raspberry Pi to a Windows desktop, and has more articles written about it than any other VPN out there. It’s the diesel truck of networking—reliable, proven, and built to last through the apocalypse.
WireGuard showed up in 2015 and basically said, “What if we made a VPN that didn’t suck?” It’s lean, fast, and simple. In 2026, if you’re setting up a VPN from scratch, there’s almost no reason to pick OpenVPN anymore. Let me explain why.
The Code Volume Problem
OpenVPN’s codebase is roughly 600,000 lines of code. It’s massive, complex, and built on OpenSSL—which is itself a hall of mirrors of legacy protocols, ancient compatibility layers, and decades of CVEs. Every time OpenSSL gets patched, OpenVPN admins hold their breath.
WireGuard? About 4,000 lines of kernel code. The entire thing fits in your head. It uses modern cryptography (Curve25519, ChaCha20-Poly1305, BLAKE2) instead of relying on ancient OpenSSL infrastructure. Smaller attack surface, fewer bugs, easier audits. Seriously, the original WireGuard paper was published in the IEEE and got read by actual cryptographers who didn’t find anything to complain about.
Real-World Performance
OpenVPN running in userspace can saturate a gigabit link, but you’re fighting CPU overhead the whole way. It’s doing encryption/decryption in application space, context-switching between user and kernel mode. Not terrible, but not optimal.
WireGuard runs in the Linux kernel (and is available as userspace implementations for other OSes). On equivalent hardware:
- Throughput: WireGuard does 1.3–1.4 Gbps on a single core. OpenVPN on equivalent hardware tops out around 500–600 Mbps.
- Latency: WireGuard adds ~1–2ms overhead. OpenVPN adds 5–10ms depending on your compression and cipher settings.
- CPU: WireGuard idles at nearly zero. OpenVPN’s daemon stays warm even when idle.
For a home lab? You won’t notice. For serious throughput—serving Plex across continents, moving backups over the VPN, hosting a game server—WireGuard wins by a landslide.
Setup Complexity: A Tale of Two Configs
Let’s say you want to set up a simple point-to-site VPN where one peer connects to a central hub.
OpenVPN (hub side):
port 1194proto udpdev tunca ca.crtcert server.crtkey server.keydh dh.pemserver 10.8.0.0 255.255.255.0ifconfig-pool-persist ipp.txtkeepalive 10 120cipher AES-256-CBCauth SHA256tls-version-min 1.2tls-cipher DEFAULT:!aNULLcompress lz4push "route 192.168.1.0 255.255.255.0"push "redirect-gateway def1 bypass-dhcp"user nobodygroup nogrouppersist-keypersist-tunstatus openvpn-status.loglog-append openvpn.logverb 3mute 20And you need to generate certificates with easyrsa, manage keys, and the client config is a whole separate headache.
WireGuard (hub side):
[Interface]Address = 10.0.0.1/24ListenPort = 51820PrivateKey = (hub private key here)PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADEPostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
[Peer]PublicKey = (client public key here)AllowedIPs = 10.0.0.2/32Client side? Even simpler:
[Interface]Address = 10.0.0.2/24PrivateKey = (client private key here)DNS = 1.1.1.1
[Peer]PublicKey = (hub public key here)Endpoint = vpn.example.com:51820AllowedIPs = 10.0.0.0/24, 192.168.1.0/24PersistentKeepalive = 25Generate keys with wg genkey, paste them in. Done. No certificate authorities, no DH parameters, no OpenSSL nonsense.
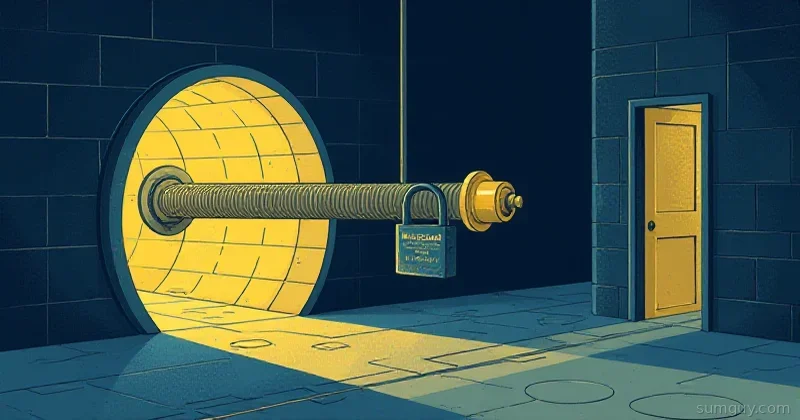
Cryptography Without the Theater
OpenVPN can use any cipher you throw at it—which sounds great until you realize that choice is a liability. You’re picking from algorithms of varying quality, some older than the problems they solve. It’s designed for maximum compatibility, which means maximum complexity.
WireGuard baked in one set of cryptographic algorithms, chosen by someone who actually reads papers:
- Key exchange: Elliptic Curve Diffie-Hellman over Curve25519 (modern, fast, 128-bit security)
- Symmetric cipher: ChaCha20-Poly1305 (designed by DJB, faster than AES on CPUs without AES-NI)
- Hash: BLAKE2 (faster than SHA-2, just as secure)
No negotiation, no downgrade attacks, no “which algorithm combo is secure in 2026?” It’s already decided. That’s not a limitation—that’s good design.
The Roaming Problem
Your laptop closes. Your WiFi router restarts. Your IP address changes. What happens?
OpenVPN: Has to re-establish the handshake, re-authenticate, re-negotiate keys. It’s a whole ceremony. Reconnect means downtime.
WireGuard: Stateless. Your source IP changes? Doesn’t matter. The next packet authenticates itself with a timestamp. Send a packet from any IP and the peer accepts it. Roaming is seamless.
This is why every mobile VPN service starting to switch to WireGuard-based solutions. Your phone can jump from WiFi to 5G without dropping the connection.
When OpenVPN Still Makes Sense
Be honest though: WireGuard isn’t a universal replacement. Yet.
- TCP-only firewalls: Some corporate networks block UDP entirely. OpenVPN over TCP works (barely). WireGuard? UDP-only.
- Ancient clients: If you’ve got Windows 7 machines that need to connect, WireGuard’s client support is still playing catch-up.
- Regulatory theater: Some enterprises have “we use OpenVPN” written into compliance documents. Changing it means paperwork.
- UDP unreliability on specific networks: Rare, but some ISPs have UDP issues. OpenVPN’s TCP fallback is genuine value.
The Ecosystem
WireGuard caught the industry’s attention fast. Now you’ve got:
- Tailscale: Managed WireGuard with magic DNS and ease-of-use that makes home-lab folks weep with joy. Overkill for a personal setup, perfect for multiple offices.
- Headscale: Self-hosted Tailscale equivalent. Open source, runs on your hardware.
- WireGuard-UI / wg-easy: Simple web interfaces for managing peers without editing configs by hand.
These tools exist because WireGuard’s simplicity makes them possible. You can’t build a “one-click OpenVPN” without fighting complexity.
The Verdict
Pick WireGuard if:
- You’re setting up a new VPN from scratch
- Performance matters even a little
- You like not having to debug OpenSSL
- Your clients can run WireGuard (Linux, macOS, iOS, Android, Windows, FreeBSD)
Pick OpenVPN if:
- You’re in a corporate environment that mandates it
- You need TCP-fallback for a hostile network
- You’re maintaining an existing setup and rip-and-replace isn’t worth it
- Your firewall blocks UDP and you can’t change it
For everything else in 2026? WireGuard wins. It’s faster, simpler, and doesn’t make you hate networking. That’s basically all you need to know.