Posts
Page 22 of 41
-
SSH Keys in 2026: Ed25519 Is the Standard
RSA SSH keys are aging out. Why Ed25519 is the 2026 default, how to generate one in 30 seconds, and how to audit and rotate your legacy keys safely.
9 min read -
Text Generation Web UI vs KoboldCpp: Power User LLM Interfaces
Compare Text Generation Web UI and KoboldCpp for local LLM inference. Covers setup, model formats, APIs, samplers, performance, and which tool fits your workflow best.
15 min read -
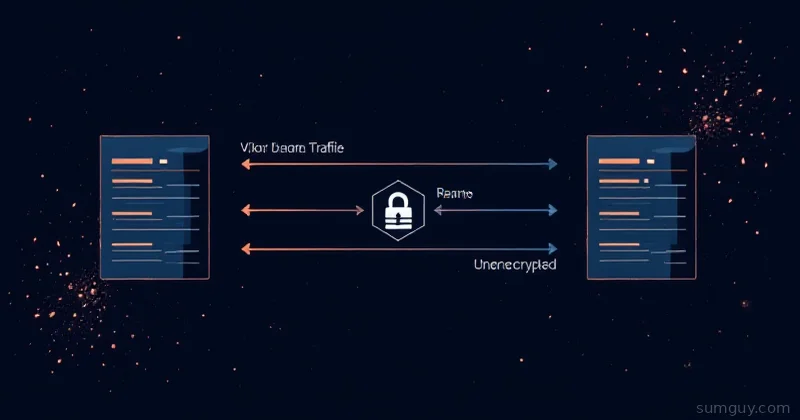
Why Your VPN Isn't Routing What You Think
You enabled the VPN but half your traffic still bypasses it. Here's why and how routing actually works.
6 min read -
Your First Open Source Contribution: Less Scary Than You Think, More Useful Than You Know
Make your first open source contribution without embarrassing yourself. Find good first issues, fork correctly, write real PR descriptions, and handle review like a pro.
7 min read -
Watchtower vs Diun: Automating Docker Updates Without Burning Your Stack
Compare Watchtower and Diun for Docker container updates. Learn which auto-update tool fits your homelab with Compose examples, notifications, and filtering tips.
13 min read -
Uptime Kuma: Status Pages, Alerts, and Knowing Before Your Users Do
Advanced Uptime Kuma setup: TCP/DNS/Docker monitors, push monitors, Telegram alerts, public status pages, maintenance windows, and Docker Compose with backups.
9 min read -
Watchtower: Safe Container Auto-Updates
Tired of manually updating containers? Watchtower handles it. But if you set it wrong, you'll wake up to broken apps. Here's how to do it right.
5 min read -
Chaos Engineering: Break Things on Purpose Before They Break Themselves
Learn chaos engineering with Pumba for Docker container chaos and Toxiproxy for network failure simulation. Discover failures in staging before your users find them in production.
9 min read -
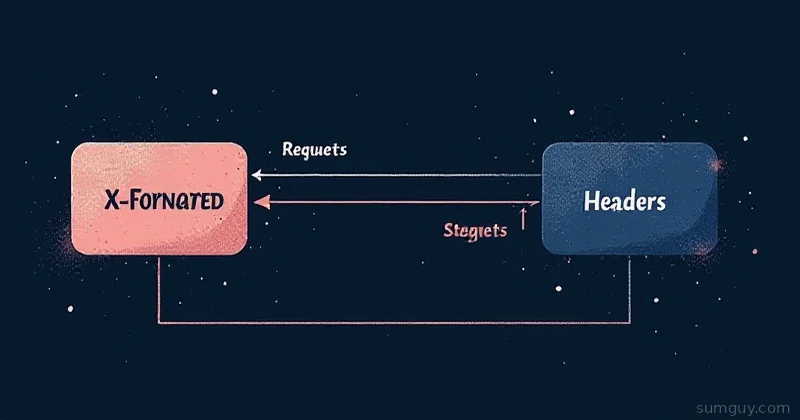
The Header Your Reverse Proxy Keeps Dropping
Your backend can't see the client IP because the reverse proxy silently dropped it. Here's why and how to fix it right.
5 min read -
Kernel Live Patching: Security Updates Without the 3am Reboot
Apply Linux kernel security patches without rebooting using kpatch and Canonical Livepatch. Keep servers secure and online simultaneously — here's the practical setup guide.
8 min read -
You Should Be Testing Your Restores
You've got backups. Great. But do you know if they actually work? RTO and RPO mean nothing if you've never actually restored.
5 min read -
IPv6 on Your Home Lab: You Should Care (Here's Why)
IPv6 isn't just for the future—it's broken on your network right now. Here's why you should care and how to actually set it up.
5 min read